D3 AI/ML Data Discovery & Tagging
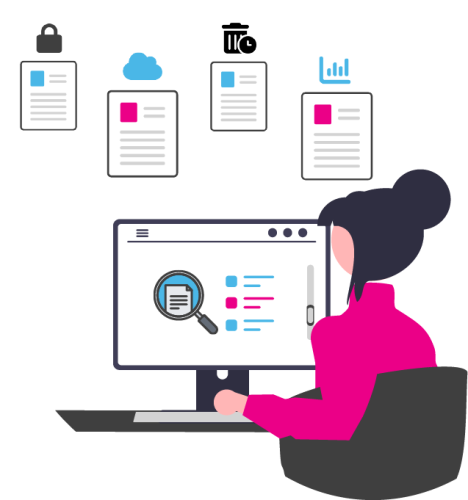
Identify and tag data for security and compliance, cloud migration, retention policies, and analytics
Check out our white paper on the data discovery foundation of Zero Trust co-authored by cybersecurity expert Chuck Brooks.
what data do you have?
where did it come from?
what important or sensitive data does it contain?
what should be done with it?
manage data using D3 AI/ML data discovery automation with metadata tagging and workflows
Solve data challenges with artificial intelligence and machine learning data discovery, tagging, and workflows
Data privacy, security & compliance
Ensure data security, privacy, and compliance using D3 Data Discovery solution to automate indexing of any data store while leaving data in place. Visualize and workflow critical data at the content level.
- Security & Privacy – Discover and tag sensitive data for security and Zero Trust. Index, filter, and find PHI and PII for privacy requests including Subject Access Requests (SARs).
- Redaction – Discover and redact data for FOIA and ROI requests.
Cloud and data migrations
Inventory and tag data stores with metadata using AI/ML D3 Data Discovery to prepare for cloud and data migrations. Classify and bulk tag records for projects using standard or custom metadata, such as file location, author, or last modified date.
We also offer digitization and classification of physical files.
Data analytics & research
Ensure data quality for data analytics and research using D3 AI/ML Data Discovery & Distillation for advanced queries and federated search. Use features like Locate Similar Files, Pattern Matching, and Word Clouds to workflow key business intelligence. Remove data duplicates and establish data lineage to reduce data analysis errors and storage costs.
Use our D3CODE solution to anonymize PHI and PII for research and analytics projects.
Data governance and retention policies
AI/ML D3 Data Discovery gives you a holistic view of your entire data estate for data governance and retention policies. Assess risk, reduce ROT (Redundant, Obsolete, Trivial) files, and workflow to create role-based access.
Reduce over-retention while maintaining compliance. User-friendly tools include drill-down on data visualizations, sensitive data risk filters, federated search, similar files, and other tools.